As the use of HTTPS continues to increase across the Web, we need more support from Certificate Authorities that issue the certificates to make it all work. I'm a huge fan of Let's Encrypt and what they're doing, but if we want to encrypt the entire Web, we can't rely and depend on a single organisation to help us do that. That's why I'm happy to announce another free CA to help us get there!
Existing Options
Of course, Let's Encrypt is my primary recommendation when anyone asks me about a CA. They're free to use, simple and reliable. Something else I always tell everyone though, especially in our TLS/PKI Training, is that you should have a backup CA. Your certificate makes your website work, and if your certificate stops working, your website stops working! There are many reasons a certificate can stop working, with the usual one being expiration, but the fact remains you need a new one. Now, if Let's Encrypt are having a bad day and you can't get a certificate from them for whatever reason, you have a problem. This is why a backup CA is so important, we must have other options.
I've previously spoken about two other CAs that offer free certificates via an ACME API, Buypass and ZeroSSL. You can see the blog posts about each of those two CAs linked there, but today I'm focusing on another option we now have.

SSL.com
We can now bring the total number of CAs that you can use quickly, easily and for free up to four! There are a couple of steps to setup an account on SSL.com, here's how.
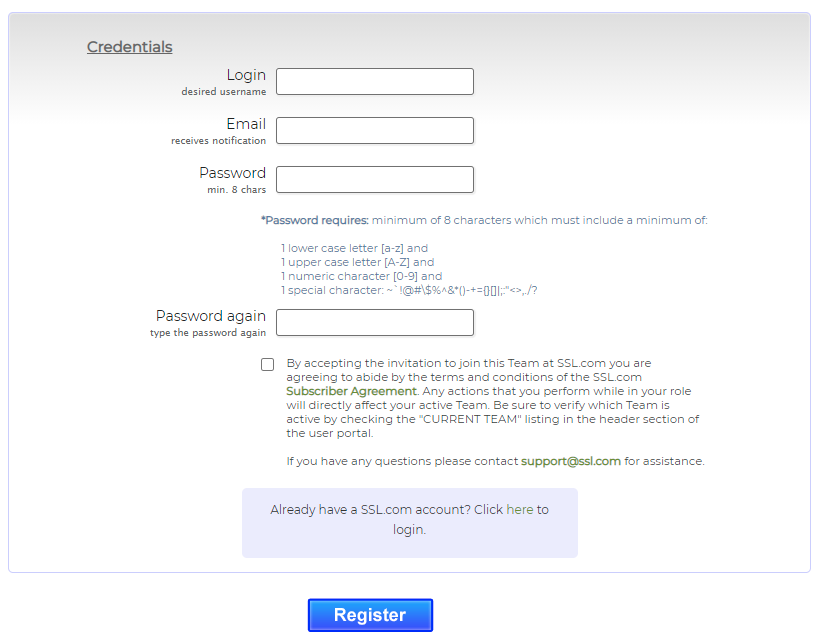
First, register for a free account.
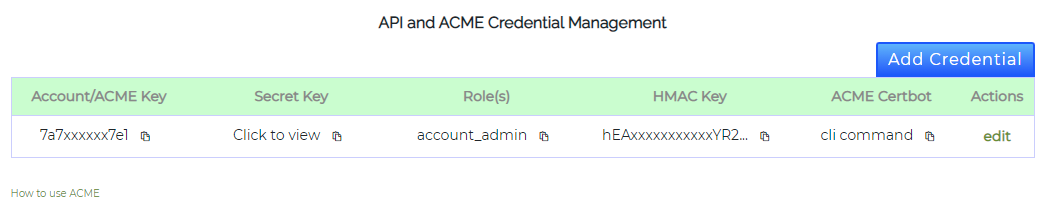
Next, you need to get your API credentials so your ACME client can talk to their API. You can get those here.
Now you can register your ACME client with the SSL.com API. I'm using the acme.sh client but the process will be similar no matter which client you choose to use. This is the first command to run to register an RSA account.
scott@Middle-Earth:~$ acme.sh --register-account --server sslcom -m scotthelme@hotmail.com --eab-kid 7a7xxxxxx7e1 --eab-hmac-key h
EAxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxGzs
[Sat 14 Aug 10:29:57 UTC 2021] Create account key ok.
[Sat 14 Aug 10:29:58 UTC 2021] Registering account: https://acme.ssl.com/sslcom-dv-rsa
[Sat 14 Aug 10:30:01 UTC 2021] Registered
[Sat 14 Aug 10:30:01 UTC 2021] ACCOUNT_THUMBPRINT='fB-V5_I03s_SLVnsn_ldKxxxxxxxxxxxxxxxxxxxOnY'Followed by the second command to register an ECC account.
scott@Middle-Earth:~$ acme.sh --register-account --server sslcom -m scotthelme@hotmail.com --eab-kid 7a7xxxxxx7e1 --eab-hmac-key hEAxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxGzs --ecc
[Sat 14 Aug 10:30:13 UTC 2021] Registering account: https://acme.ssl.com/sslcom-dv-ecc
[Sat 14 Aug 10:30:16 UTC 2021] Registered
[Sat 14 Aug 10:30:16 UTC 2021] ACCOUNT_THUMBPRINT='dghxxxxxxxxxxxxxxxxxxTlA__VN1xxxxxxxxxxxnPk'You're now ready to go and issue some certificates!!
/home/scott/acme.sh/acme.sh --issue --dns dns_cf -d sslcom-demo.scotthelme.co.uk --force --keylength ec-256 --server sslcomSubject: CN=sslcom-demo.scotthelme.co.uk
Issuer: CN=SSL.com SSL Intermediate CA ECC R2,O=SSL Corp,L=Houston,ST=Texas,C=US
-----BEGIN CERTIFICATE-----
MIIE3jCCBGSgAwIBAgIQXwe4TbSr/OT1NIJdzXuvajAKBggqhkjOPQQDAzBvMQsw
CQYDVQQGEwJVUzEOMAwGA1UECAwFVGV4YXMxEDAOBgNVBAcMB0hvdXN0b24xETAP
BgNVBAoMCFNTTCBDb3JwMSswKQYDVQQDDCJTU0wuY29tIFNTTCBJbnRlcm1lZGlh
dGUgQ0EgRUNDIFIyMB4XDTIxMDgxOTA5MTE1N1oXDTIxMTIwMTA5MTExNVowJzEl
MCMGA1UEAwwcc3NsY29tLWRlbW8uc2NvdHRoZWxtZS5jby51azBZMBMGByqGSM49
AgEGCCqGSM49AwEHA0IABHUP4CFgZPXy8uZ7DsACKX3vs3vilM3TEU89quR1DoL7
1O7V0FtBHcs7qYL8IQVI7kHs+XTFepdj2HJkVmjr4IijggMoMIIDJDAfBgNVHSME
GDAWgBQNdGYKXp/iLOzVwl0lBH91Mrr/fTBxBggrBgEFBQcBAQRlMGMwPwYIKwYB
BQUHMAKGM2h0dHA6Ly9jZXJ0LnNzbC5jb20vU1NMY29tLVN1YkNBLVNTTC1FQ0Mt
Mzg0LVIyLmNlcjAgBggrBgEFBQcwAYYUaHR0cDovL29jc3BzLnNzbC5jb20wJwYD
VR0RBCAwHoIcc3NsY29tLWRlbW8uc2NvdHRoZWxtZS5jby51azBRBgNVHSAESjBI
MAgGBmeBDAECATA8BgwrBgEEAYKpMAEDAQEwLDAqBggrBgEFBQcCARYeaHR0cHM6
Ly93d3cuc3NsLmNvbS9yZXBvc2l0b3J5MB0GA1UdJQQWMBQGCCsGAQUFBwMCBggr
BgEFBQcDATBEBgNVHR8EPTA7MDmgN6A1hjNodHRwOi8vY3Jscy5zc2wuY29tL1NT
TGNvbS1TdWJDQS1TU0wtRUNDLTM4NC1SMi5jcmwwHQYDVR0OBBYEFIt0k8bwGO+1
n034I0dkoRWqsSZpMA4GA1UdDwEB/wQEAwIHgDCCAXwGCisGAQQB1nkCBAIEggFs
BIIBaAFmAHYA9lyUL9F3MCIUVBgIMJRWjuNNExkzv98MLyALzE7xZOMAAAF7Xbea
SwAABAMARzBFAiEAiyE1SNTQwTmRvVykP/UwEhWEQaB+OK8YgAvdB35D0noCIA2E
xp1utn71m8FVyC1hV1liUBCzH5LqXZtsyr+2xLiaAHUARJRlLrDuzq/EQAfYqP4o
wNrmgr7YyzG1P9MzlrW2gagAAAF7XbeaJwAABAMARjBEAiBajOP6SU25q66Fu764
W0oylvWsNJQ+qswm4p7eG70CUgIgbEvnjrRFMfHiCKVhhMH8EvDqd673DmJCYl+N
dia4oYEAdQDuwJXujXJkD5Ljw7kbxxKjaWoJe0tqGhQ45keyy+3F+QAAAXtdt5qV
AAAEAwBGMEQCIAE9zgcNTDbHVVY4pABhABZqKroKnz2onMLGuFYQw2WPAiBx4B46
LHySyUAid40jk5MkoF+XvqxTanBb+O02PIJoiDAKBggqhkjOPQQDAwNoADBlAjAs
FJAlEzOYGS9QGCMAvv/dsgrXCcaTtd3RMFkhiYCmP03Uk9dAmUT6TecAcmbWuHkC
MQC2LPc1hxTb85cnTm5tICB8SA3NAgo+53dLcpGoBOpioB2Fs9UhfS7b2dz6xPOC
+b8=
-----END CERTIFICATE-----One new certificate ready to go and here's the CT log in crt.sh to show it! This is super easy and only took me a matter of minutes to setup a new CA and get a certificate issued.
Randomising my CA
Just because I can and just because I'm interested, I figured I'd randomise the CA I'm using to be any one of the four that are now available to use for free via ACME. I have a little HP ProLiant server under my stairs that I use for various tasks and projects with one of them being to manage certificates for all of my internal devices. My certificate management is nothing fancy, I just have a few bash scripts running via cron that obtain new certificates and deploy them locally on the server or SCP them to where they need to be on my network devices like my UniFi Dream Machine Pro or my UniFi Protect NVR. I've now added a random selection for which CA will be used so from now on, Let's Encrypt won't be my exclusive CA!
#!/bin/bash
set -e
SERVERS=("zerossl" "letsencrypt" "buypass" "sslcom")
/home/scott/acme.sh/acme.sh --issue --dns dns_cf -d homeassistant.scotthelme.co.uk --force --keylength ec-256 --server $(shuf -n1 -e "${SERVERS[@]}")If you're using Certificate Authority Authorisation then don't forget to set the ssl.com value to let them issue certificates for your domain, but other than that, it's easy!
Update: The CAA value for this CA is ssl.com.
