We've been working on CSP Integrity for a little while now, and it was only announced in open beta back in September. Since then, as more of our customers start to use it, we've continued to improve it and observe the potentially huge benefits.

CSP Integrity
You can read the full post on CSP Integrity and how it works, but here's a quick TLDR. You can now leverage a native feature in modern browsers to have the browser send you the cryptographic fingerprint of any JavaScript that is running on your site. Once we receive that data, we can do some pretty amazing things with it, and it opens up a whole new world of possibilities. This is a fundamental shift in browser capabilities and the best part is that if it takes you more than 30 seconds to configure and deploy this, you probably did it wrong!
Our Fingerprint Database
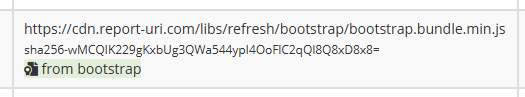
Receiving the fingerprint of all scripts that are running is great, but it's even better to have an enormous database of known fingerprints to check against, and that's something we've been working on. Our database only contains the fingerprints of known and verified files, and that verification was done by us. That means if we get a match for the fingerprint provided against our database, we can say with certainty that we know what that file is.
Our latest data is available to all customers in production right now, so if you're sending us CSP Integrity data, it's being cross-checked against our database already. This is the latest output from the process that generates our data after passing over the terabytes of JavaScript we already have:
⭐ Produced sha256 hashes:11,276,852
⭐ Produced sha384 hashes:11,276,852
⭐ Produced sha512 hashes:11,276,852
📦 33,830,556 total fingerprints
If you're using common libraries or files right now, we can start to identify and tag them in our UI with information on the source of that file, and having the ability to do this across literally millions of files really has an impact.
On top of this new capability, we of course still have all of our existing Threat Intelligence capabilities too, which leverage our own feeds of data, and external feeds from industry, to identify known bad domains and files, suspicious activity, known IoC (Indicator of Compromise) and much more.
Vulnerability mapping
When we're observing the use of thousands of different JavaScript libraries by our customers, it's obvious that some of those libraries are going to contain security vulnerabilities. Because we can identify individual files based on their fingerprint, and then map that back to which version of which library is being used, we can then gather data on any vulnerabilities that impact our customers and let them know!
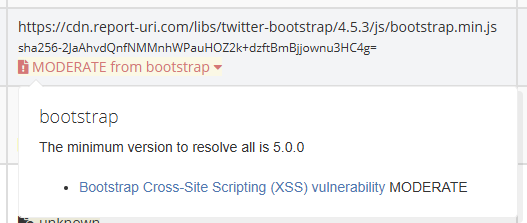
We're currently tracking hundreds of unique vulnerabilities across all of our verified libraries that impact literally thousands of files, so you can rest assured that if you're using any kind of popular library that has a know problem, we're going to detect it.
Threat Intelligence
We now regularly collect data from almost 250,000,000 unique browsers per month, that's a quarter of a billion browsers sending us data on what they're seeing on the Web. With our birds-eye view of so much activity, we can infer a lot from the data that we gather, far beyond the value that this provides to any individual customer. For example, a very simple metric that we use regularly is "For the tens of thousands of sites that use our service, have any of them ever loaded this JavaScript before?". For the answer to that question to have value, the number of sites we're protecting has to be large enough to matter, but as we continue to grow, the answer to that question is meaningful. Knowing if you're the only site in the World loading some specific JavaScript, or you're one of thousands, is a great insight to have. There are a whole variety of seemingly simple metrics like this that are incredibly valuable and we are now in a position to start leaning on this data to better protect our customers.
On top of this, we also ingest various industry feeds of Threat Intelligence data to enrich our own. Just because we haven't seen a URL behave in a malicious way just yet, it doesn't mean that someone else hasn't. By feeding in Domain Reputation Data, Malware Feeds, Phishing Campaigns, IP Reputation and more, we can look at what JavaScript you're loading and make a determination on how likely it is to be trustworthy or not.
More to come!
As always, we're continually working to improve our product to better serve our customers. If you have any feature ideas or suggestions, please do feel free to reach out to me, and keep an eye out for some of the exciting announcements coming in H1 2026!
