Many sites lead you to believe that just because there is a padlock icon in the corner of your screen, or https:// at the beginning of the address, that data being exchanged on these pages is secure. This isn't always the case.
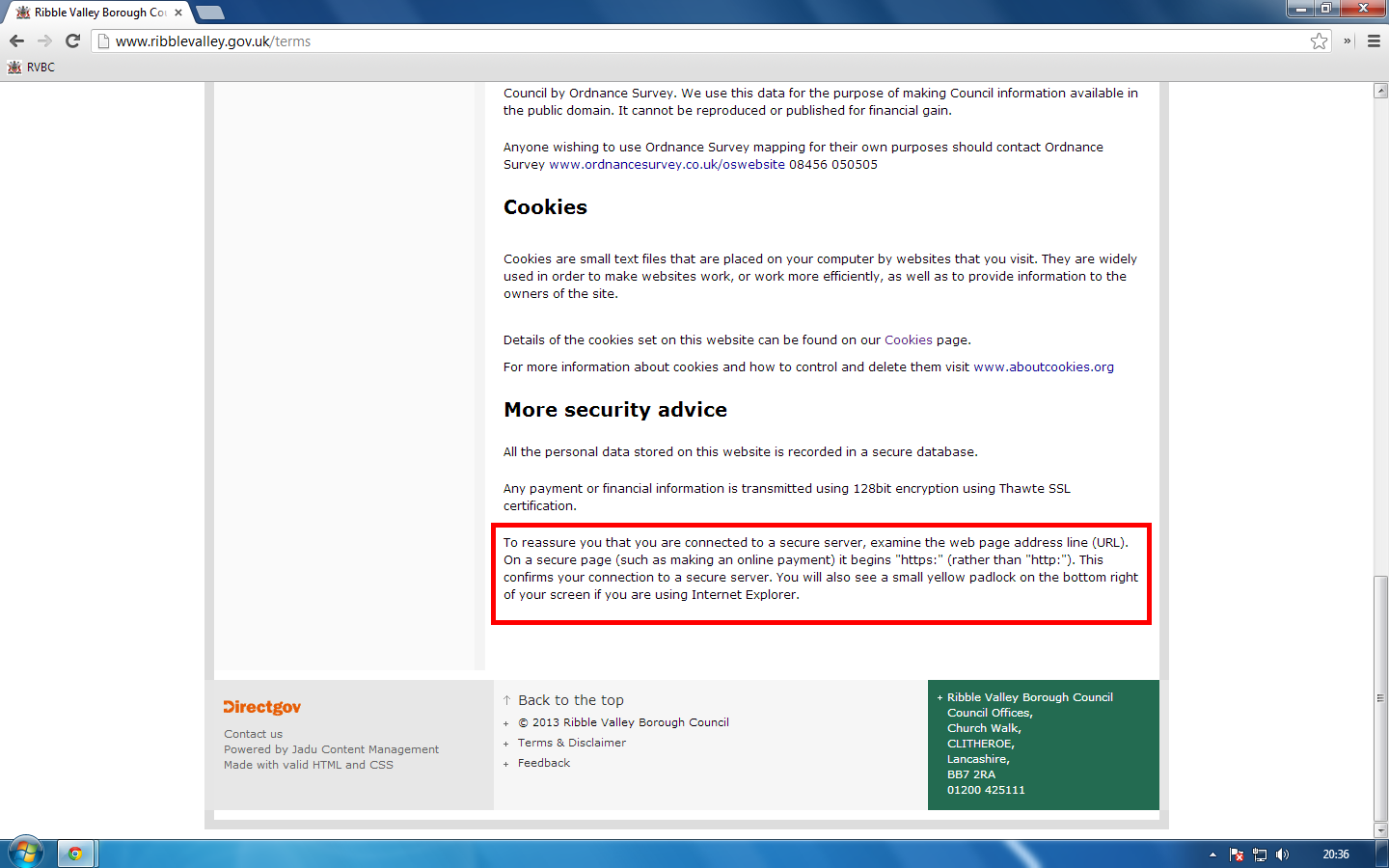
We've all seen the padlock icons, shields and security stamps on sites that we've visited giving us assurances that they are secure. Our information is encrypted and prying eyes out in the wild can't snoop on it as it makes its way around the Internet. I recently came across such a claim whilst using my local council website, the Ribble Valley Borough Council (RVBC), and thought I would demonstrate why TLS (SSL) doesn't always mean secure.
(Remember to watch in HD!)
The session hijacking attack can be prevented by using HTTPS across the entire site. Once the user is authenticated to the site no further communication should take place over HTTP and this includes loading other content. The fact that this site uses HTTPS to protect the account pages means the owners acknowledge that a man in the middle could access the data whilst it is in transit and that it needs protecting. To then continue sending the session ID over HTTP removes the protection afforded by HTTPS as this simple demonstration has shown.
You can grab yourself a copy of Wireshark HERE and have a go at sniffing packets off your own network adapter. Remember to always use these tools responsibly!
Scott.
Short URL: https://scotthel.me/SessionHijacking
